By A Mystery Man Writer
When a Merkle-Damgård based hash is misused as a message authentication code with construction H(secret ‖ message), and message and the length of secret is known, a length extension attack allows…

哈希长度拓展攻击(Hash Length Extension Attacks)
GitHub - mumubebe/lext: 🐶️ Length extension attack tool (SHA1, SHA256, SHA512, MD5)

Hash Length Extension Attacks

20 years of payment processing problems / Habr
GitHub - PortSwigger/length-extension-attacks: Length extension attacks in Burp Suite

Length Extension Attack

Length Extension Attack on MD4. In this article we will exploit a…, by Henrique Marcomini, Sinch Blog

3 Message authentication codes - Real-World Cryptography

Hash Length Extension Attack - HackTricks - Boitatech
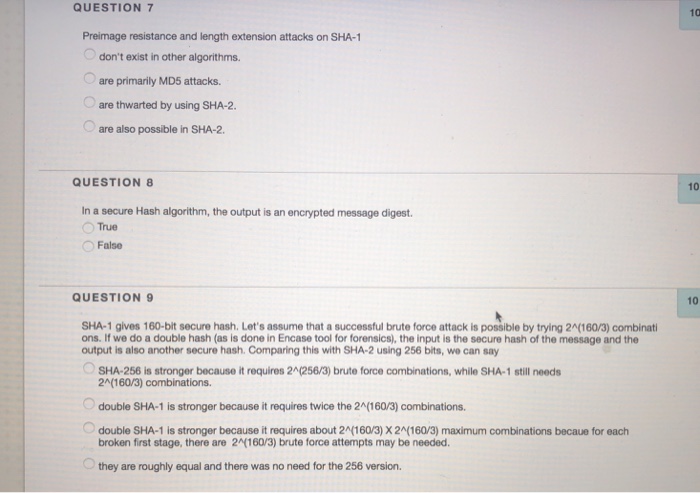
Solved QUESTION 7 Preimage resistance and length extension

Walking: [Crypto] Length Extension Attack

The Hashlib, OpenSSL and Length Extension Attacks

Intense - Hack The Box
Hash Length Extension Attacks Explained

Figure 2 from Flickr's API Signature Forgery Vulnerability